AiPrise
9 min read
November 28, 2025
How Continuous Payment Transaction Monitoring Prevents AML Risks

Key Takeaways










Could a single missed payment pattern trigger regulatory fines and enable rapid money laundering across your rails?
As a compliance leader, your team faces overwhelming alert volumes, fragmented KYC/KYB data, and investigator burnout. High-velocity payment rails and cross-border flows compress detection windows and enable structuring that evades batch controls. AFP’s 2025 survey showed 79% of organizations faced payment fraud in 2024, proving detection gaps are widespread. Continuous payment transaction monitoring narrows detection windows, reduces false positives through enrichment, and accelerates high-confidence investigator triage. Adopting continuous monitoring helps compliance teams prioritize high-risk flows and provides auditable evidence for regulators.
Quick Overview
- Continuous payment transaction monitoring tracks every payment in real time, helping detect suspicious patterns before they become AML breaches.
- Linking transactions with verified KYC and KYB data gives compliance teams full visibility into customer behavior and payment risks.
- Real-time analysis reduces false positives, improves alert accuracy, and ensures faster action on truly high-risk activities.
- Continuous monitoring builds a reliable audit trail, supporting stronger regulatory compliance and protecting institutions from costly enforcement actions.
What is Transaction Monitoring?
Transaction monitoring helps detect suspicious or unusual payment activity across your systems before it turns into a compliance issue. It tracks transaction patterns, values, and counterparties to reveal behavior that doesn’t align with a customer’s normal activity. Each transaction ties back to verified identity data, giving your compliance team the clarity needed to flag risks faster. This ongoing visibility keeps financial operations safer and builds confidence in your institution’s AML controls.
Having defined the process, it’s worth understanding how specialized AML systems make this monitoring smarter and faster.
What is Transaction Monitoring in AML?
A transaction monitoring system in AML helps track payments as they happen, spotting unusual or suspicious patterns tied to high-risk behavior. It collects transaction data, adds verified KYC and KYB details, and runs checks through rule-based and behavioral models to catch red flags quickly. Investigators in your team see each alert with a full record of related evidence and a clear risk score for review. Transparent alerts matter because regulators expect clear reasoning, and near-real-time systems give your team that visibility before risky payments clear.
Knowing how these systems operate raises another question: why are they such a vital part of AML compliance?
Also read: Microstructuring: Challenges in AML Compliance
Why Transaction Monitoring Matters for AML Regulatory Compliance?
Transaction monitoring forms the foundation of AML compliance by helping detect suspicious activities before they turn into regulatory violations.
Here are the key ways it supports compliance programs across financial institutions:
- Tracks transactions in real time to identify unusual patterns that may indicate layering or structuring.
- Connects customer activity to verified KYC and KYB data, creating a complete audit trail for regulators.
- Flags high-risk transactions automatically, ensuring timely reporting of suspicious activity.
- Reduces manual errors by standardizing alerts and evidence gathering for AML reviews.
- Demonstrates continuous oversight, which regulators often expect during examinations and audits.
While compliance is the anchor, transaction monitoring also brings real operational value when applied across diverse payment use cases.
Transaction Monitoring Use Cases
Transaction monitoring applies across different industries and payment systems to uncover hidden risks and suspicious movements. Here are some of the most common use cases:
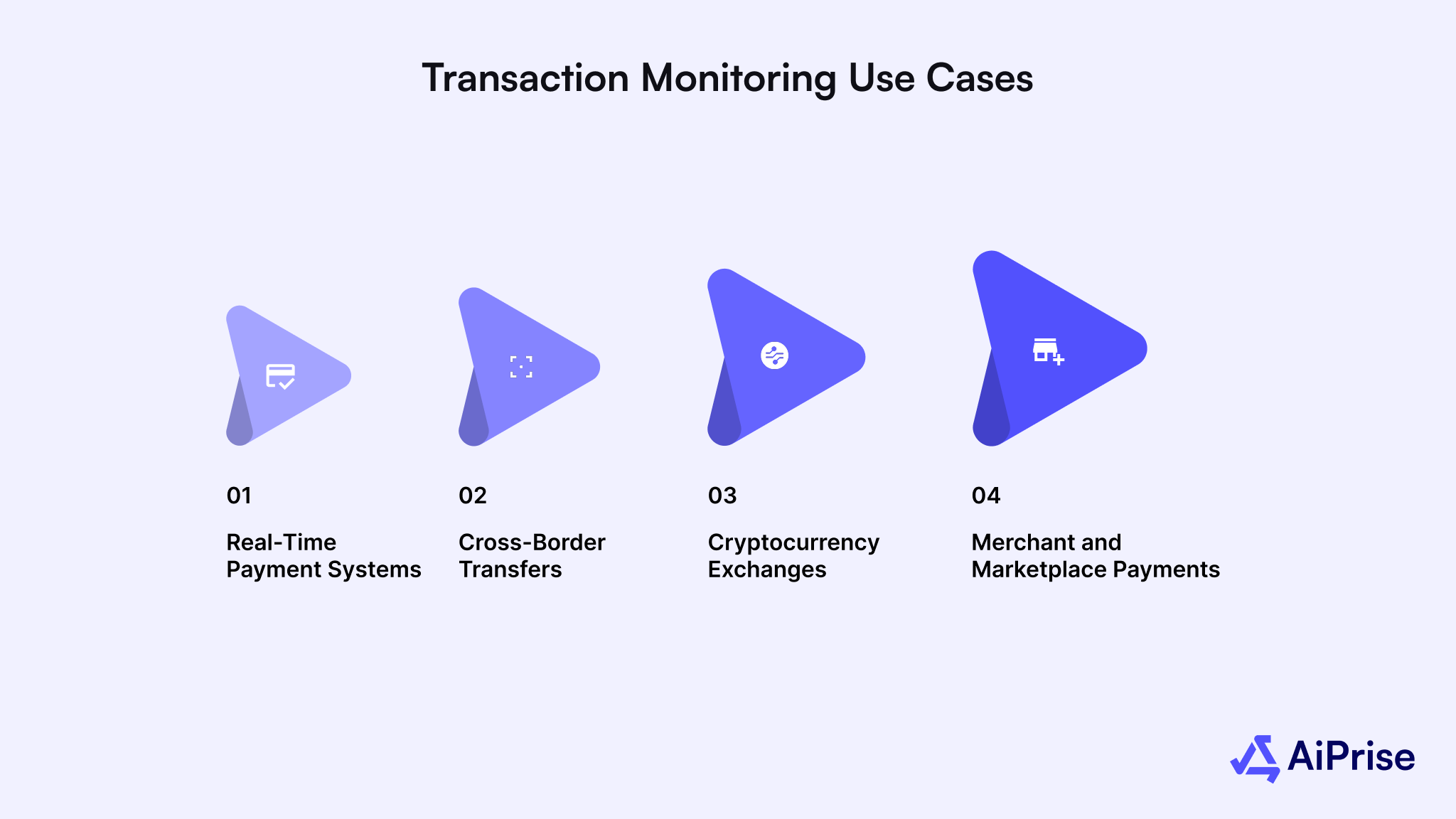
1. Real-Time Payment Systems
Monitoring high-speed payments helps compliance teams detect suspicious velocity patterns and prevent funds from leaving before review. It narrows the time gap between transaction initiation and investigation, which is vital in instant payment environments. Clear risk scoring helps investigators act faster and reduce post-settlement remediation.
2. Cross-Border Transfers
Continuous checks on cross-border flows reveal anomalies like repeated transfers to high-risk regions or unverified beneficiaries. They also detect structuring across multiple accounts meant to disguise the true source of funds. Having visibility at this level prevents violations of regional and global AML laws.
3. Cryptocurrency Exchanges
Monitoring blockchain-based transactions identifies patterns linked to mixing services, high-risk wallets, or sanctioned addresses. It also ensures crypto platforms comply with Travel Rule obligations and suspicious activity reporting standards. Integrating KYT (Know Your Transaction) data with AML monitoring gives a full view of digital asset movement.
4. Merchant and Marketplace Payments
Transaction monitoring helps payment processors and marketplaces uncover suspicious merchant behavior, such as fake refund loops or synthetic identities. It also verifies whether merchant payouts align with legitimate sales activity. These checks safeguard both consumers and financial partners from fraud and regulatory penalties.
These use cases show how broad monitoring can be, but what actually powers it beneath the surface? Let’s look at the mechanics.
Also read: Comprehensive Guide to AML Compliance in FinTech
How Does Transaction Monitoring Work?
Transaction monitoring works by analyzing every payment that moves through your system to detect suspicious activity before it turns into a compliance risk. It connects transaction data, customer information, and behavioral patterns to spot red flags that might indicate money laundering or fraud.

Here’s how the process usually works in practice:
1. Data Ingestion
This stage focuses on collecting all payment data from different systems and channels so nothing is missed during analysis. Here’s what happens at this point:
- Every transaction, amount, time, location, sender, and receiver is captured from payment rails and internal systems.
- Data is collected from multiple sources such as banks, card networks, and third-party processors.
- Real-time collection ensures your team can analyze ongoing transactions without delays or blind spots.
2. Enrichment and Profiling
This step adds background information to every transaction, making it easier to understand who is behind it and whether it looks normal. Here’s what it involves:
- Customer identity and business registration data from KYC and KYB processes are linked to each payment.
- Past transaction behavior is compared to new activity to identify sudden spikes or unusual changes.
- External data, such as sanctions lists, watchlists, and adverse media checks, strengthen risk scoring.
3. Detection and Scoring
At this stage, the system checks transactions for signs of suspicious activity and assigns a risk score based on what it finds. Here’s how this step works:
- Rule-based models flag activity that breaks established limits, like large transfers or repeated small payments.
- Behavioral and machine learning models look for deviations from normal spending or transfer habits.
- Each flagged transaction receives a real-time risk score that helps your team focus on the most urgent alerts.
4. Case Management and Feedback
This final stage helps compliance teams review, resolve, and learn from alerts so the system keeps improving.
Here’s what happens here:
- Investigators examine each alert with supporting evidence such as linked accounts or related payments.
- Confirmed suspicious activity is escalated for further action or regulatory reporting.
- Feedback from investigations is used to refine detection rules and reduce false positives in future monitoring.
Once you understand the workflow, it becomes easier to see where AML systems differ from anti-fraud systems and how the two can complement each other.
Anti-Fraud vs. AML Transaction Monitoring Systems
Anti-fraud and AML monitoring systems both safeguard transactions, but focus on different goals and signals.
Here’s a quick comparison to help clarify their roles:
Both systems work best when integrated, allowing fraud insights to inform AML detection and vice versa, building a unified defense across your payment ecosystem. Fraud and AML systems serve different purposes but together create a stronger, more dependable monitoring framework.
Also read: Understanding The Five Pillars Of An AML Compliance Program
The Role of Continuous Monitoring in Preventing AML Risks
Continuous monitoring keeps a constant track of payments to identify suspicious activity before it becomes a compliance issue. It helps compliance teams stay ahead of money-laundering risks by reviewing every payment in real time instead of waiting for end-of-day reports.
Here’s how continuous monitoring helps prevent AML risks in real-world payment environments:
1. Detects Suspicious Activity in Real Time
Continuous systems watch every payment as it happens, flagging transactions that look unusual for a particular customer or business. For example, if a small retailer suddenly sends multiple large international payments within minutes, the system alerts investigators before the money clears. This quick response helps stop potential layering or structuring attempts that might otherwise go unnoticed until it’s too late.
2. Connects Identity Data with Payment Behavior
Every payment links back to verified KYC or KYB details, giving your team a complete view of who’s behind each transaction. Suppose a customer verified as a low-income individual suddenly receives high-value wire transfers from unfamiliar regions, continuous monitoring ties that activity to their profile, and flags it instantly. This connection between identity and behavior helps your team trace suspicious funds with accuracy and act before risks escalate.
3. Reduces False Positives and Improves Accuracy
Older systems often trigger alerts for harmless activities, such as frequent small transfers between personal accounts. Continuous monitoring uses behavioral models that learn normal activity patterns and highlight only what truly looks suspicious. For instance, if a business regularly pays suppliers abroad, those transactions stop generating alerts over time, allowing investigators to focus on genuinely abnormal behavior instead.
4. Strengthens Audit Readiness and Regulatory Confidence
Every alert, decision, and resolution is automatically recorded within the monitoring system, creating a transparent trail for auditors and regulators. Imagine facing an audit where an examiner asks why a certain alert was cleared. Continuous monitoring provides timestamps, reviewer notes, and evidence in one place. Having this detailed record builds trust with regulators and demonstrates that your institution maintains active oversight over every payment flow.
These capabilities form the base of modern AML defenses, but bringing them together requires strong technology and unified systems, which is exactly where AiPrise helps.
How AiPrise Strengthens Continuous Payment Transaction Monitoring
AiPrise helps financial institutions, payment providers, and crypto platforms build continuous monitoring systems that detect suspicious activity faster and meet AML regulations with confidence. It brings together identity verification, real-time risk analysis, and automation so your team can focus on investigation rather than chasing incomplete data.
Here’s how AiPrise supports continuous transaction monitoring and reduces AML risks across your payment workflows:

- Real-time identity and business verification: Confirms customer and merchant authenticity through KYC and KYB checks powered by AI, ensuring every transaction is tied to a verified source before processing.
- Integrated AML and fraud detection engine: Analyzes payment behavior using 100+ global data sources and highlights risks like layering, unusual transfers, or sanctioned entities within seconds.
- Automated compliance workflows: Monitors transactions continuously, screens them against global sanctions lists, and updates records automatically as regulations evolve.
- Advanced biometric and document verification: Uses facial and fingerprint recognition along with OCR document scanning to prevent account misuse and impersonation in payment networks.
- Seamless system integration: Connects easily with existing payment gateways or core banking systems through APIs and SDKs, enabling near real-time transaction monitoring without disrupting operations.
- Continuous risk assessment: Tracks customers and merchants over time, detecting behavioral shifts that may indicate emerging AML risks.
Wrapping Up
Continuous payment transaction monitoring has become the difference between early detection and costly regulatory fallout in today’s payment landscape. Real-time visibility allows compliance teams to trace unusual patterns, strengthen oversight, and reduce investigation delays across fast-moving payment channels. Building this capability ensures your institution stays ahead of evolving money-laundering tactics and maintains trust with regulators and customers alike.
AiPrise simplifies that journey by combining identity verification, AI-driven risk detection, and automated AML workflows into one connected platform. Its continuous monitoring tools help your team detect anomalies faster, verify counterparties instantly, and maintain complete compliance visibility.
Book A Demo today to experience how AiPrise can modernize your transaction monitoring and keep your payment network protected.
Frequently Asked Questions (FAQs)
1. What is payment transaction monitoring?
Payment transaction monitoring is the process of tracking and analyzing financial transactions in real time to identify unusual or suspicious activity. It helps detect behaviors that may indicate fraud, money laundering, or other financial crimes. By continuously reviewing transactions against customer profiles and risk indicators, institutions can spot red flags before funds move beyond control.
2. How does transaction monitoring differ from sanctions screening?
Transaction monitoring focuses on detecting suspicious behavior or patterns within payment activity, such as rapid transfers or abnormal transaction volumes. Sanctions screening, on the other hand, checks names, entities, and counterparties against global sanctions or watchlists. Both work together, screening blocks prohibited parties, while monitoring identifies suspicious activity among approved customers.
3. What data is required for effective transaction monitoring?
Effective monitoring depends on accurate, comprehensive data that connects transactions to verified customer information. This includes KYC and KYB details, transaction amounts, account numbers, geolocation data, and payment timestamps. Adding external data, like sanctions lists or adverse media, improves accuracy and reduces the chance of missing hidden risks.
4. How quickly must monitoring detect suspicious activity for instant payments?
For instant or real-time payments, detection must occur within seconds of a transaction being initiated. Delayed detection can allow high-risk payments to settle before investigation begins, making recovery almost impossible. Continuous monitoring systems are designed to process transactions and generate alerts immediately, ensuring compliance teams can act without delay.
5. How can you reduce false positives without losing detection quality?
Reducing false positives starts with improving data quality and ensuring accurate KYC and KYB information. Using behavior-based models alongside rules-based detection helps distinguish genuine activity from suspicious patterns. Regularly reviewing and fine-tuning alert thresholds keeps monitoring precise while maintaining strong AML coverage.
You might want to read these...

AiPrise’s data coverage and AI agents were the deciding factors for us. They’ve made our onboarding 80% faster. It is also a very intuitive platform.





















.png)


.png)








.png)