November 25, 2025
Recognizing Common Banking and AML Red Flags

Key Takeaways










Have you ever approved an account that felt legitimate but later triggered serious compliance concerns?
You face onboarding friction, rising fraud, overwhelming false positives, and costly regulatory fines that strain compliance teams' resources. In 2025, FinCEN reported that U.S. institutions filed 4.7 million SARs in FY24, averaging 12,870 per day. Knowing common red flags and strengthening KYC reduces false positives, prevents fraud, and limits regulatory exposure. Read on to learn practical, bank-focused steps you can apply immediately to protect your institution.
Quick Overview
- Detecting banking red flags early helps prevent fraud, reduce compliance breaches, and protect your institution from costly penalties.
- Understanding key U.S. AML regulations, from the Bank Secrecy Act to FinCEN’s recent advisories, strengthens your compliance foundation.
- Building effective KYC and AML programs requires proper ID collection, ongoing monitoring, and dynamic risk assessment to catch anomalies faster.
- Modern, data-driven monitoring systems outperform traditional models by identifying hidden transaction patterns, reducing false positives, and improving audit readiness.
What are Banking Red Flags?
Banking red flags are operational indicators that suggest increased risk requiring immediate review and verification.
They surface during onboarding, account lifecycles, or transaction monitoring when patterns deviate from expected customer behavior. You should treat these signals as prompts to gather evidence, reassess risk, and escalate appropriately to investigators.
Recognizing them is only the first step; understanding why they matter helps determine how deeply they affect your compliance framework.
Why banking red flags matter?
Banking red flags signal operational anomalies that require immediate investigation to prevent fraud and regulatory breaches. Below are critical reasons why detecting banking red flags protects operations, compliance, and customer trust:
- Unchecked banking red flags can trigger large regulatory fines, disrupting operations and draining your capital reserves.
- Missed indicators enable fraudsters to exploit weak KYC controls, resulting in direct losses and reputational damage to your firm.
- High false positives from poor detection models overwhelm analysts and slow remediation, reducing your team's investigation capacity.
- Sophisticated schemes like funnel accounts hide through many small transfers, evading static thresholds in your transaction monitoring.
- Opaque ownership structures frustrate investigations and delay action, especially when UBO verification is incomplete within your process.
- Persistent compliance failures erode customer trust and make it harder for your institution to maintain partnerships.
To stay ahead of these risks, it’s essential to understand how U.S. AML regulations have evolved and shaped modern banking oversight.
U.S. AML Regulatory Timeline
This timeline shows major U.S. AML milestones that shape how you detect and respond to banking red flags.
Below are key regulatory milestones and obligations your compliance program must reflect to remain effective and audit-ready.
- The Bank Secrecy Act created reporting obligations and recordkeeping that force banks to watch for suspicious transactions. Over time, regulators expanded expectations, so your AML program must incorporate reporting and monitoring duties.
- The USA PATRIOT Act strengthened customer identification checks and significantly broadened suspicious-activity reporting across banking channels. Given these legal changes, your onboarding and SAR processes must remain documented, tested, and auditable by examiners.
- FinCEN’s Customer Due Diligence rule required banks to identify beneficial owners and keep clear ownership records. Failure to gather accurate UBO data creates investigative gaps you will struggle to close during suspicious-activity probes.
- The Corporate Transparency Act introduced beneficial-ownership reporting to FinCEN, increasing transparency into shell companies and nominee ownership.
As a result, your compliance workflows must align with BOI reporting rules and verify data before filing. - Recent FinCEN advisories and enforcement actions emphasize continuous monitoring, transaction testing, and robust KYC controls for banks. In practice, your teams must perform testing and update detection models to capture evolving banking red flags reliably.
Regulations set the framework, but your frontline control begins with verifying identities and documents correctly.
Also read: Anti Money Laundering (AML) Law: A Complete Guide
Essential IDs And Documents To Collect
Collecting the right IDs and documents prevents banking red flags and speeds accurate risk assessments during onboarding.
Below are the required individual and business documents that strengthen KYC, KYB, and ongoing AML controls.
- Government-issued photo ID, such as a passport or driver’s licence, is essential and must be verified robustly.
Proof of address and liveness checks help confirm identity and reduce synthetic or stolen identity risks. - Incorporation documents and articles of association provide legal existence and registration details that banks must verify. Recent bank statements or audited financials demonstrate transactional behavior and validate stated business activity and scale.
- Collecting UBO names, ownership percentages, and government IDs closes gaps that criminals use to hide control.
Verify relationships through corporate registries and third-party data to reduce opacity and investigative delays for your team. - Source-of-funds documentation, like payment traces, contracts, or bank statements, helps establish legitimacy for high-value accounts. Requesting these documents upfront prevents suspicious gaps and speeds investigations if red flags later emerge.
- Device fingerprinting, IP history, and biometric hashes add contextual signals that complement document verification in real time. These signals help detect account takeover attempts and link suspicious activity across multiple accounts or channels.
- Maintain document retention and schedule periodic revalidation to ensure records support investigations and regulatory examinations. Refreshing customer data every 12–24 months reduces stale information and helps catch identity drift or ownership changes.
Once these identification layers are in place, it becomes easier to spot early warning signs that indicate higher financial crime risk.
Major Banking Red Flags
Spotting major banking red flags early protects your institution from financial losses, regulatory penalties, and reputational harm. Here are ten critical patterns that reveal hidden risks across customer onboarding, transactions, and ongoing monitoring:

1. Inconsistent Customer Data
When a customer gives vague answers or contradictory data during onboarding, the risk of hidden intent multiplies; such behavior may indicate identity fraud, synthetic identities, or shell entities designed to bypass controls. You should escalate any account where documentation, ownership, or business purpose doesn’t align with expected patterns.
2. Unusual Transaction Volumes
Rapid, large amounts of inbound funds and immediate outbound transfers outside the business model hint at layering or funneling. Transactions significantly deviate from a customer’s known profile, strip out logic, and may signal illicit funds. Your monitoring must spot these anomalies and trigger case reviews; awaiting manual detection only increases exposure.
3. Complex Ownership Structure
Multi-layered companies, frequent beneficial-owner changes, or opaque trusts can mask true control and hide risks. When you struggle to identify a UBO or entity’s business purpose, your bank is exposed to undisclosed liabilities. Strong KYB and entity graph analysis help cut through the complexity and reduce “unknown control” blind spots.
4. High-Risk Jurisdictions
Accounts linked to sanctioned, high-corruption, or weak-supervision jurisdictions amplify your risk and compliance burden. A customer transferring funds through or from such jurisdictions demands enhanced due diligence and monitoring. You must map geography-based risk into your detection rules and escalate suspicious links quickly.
5. Documentation Anomalies
If submitted documents are forged, expired, inconsistent, or lack credible verification, the identity check fails. Missing proof of address or suspicious photo/ID mismatches allow fraudsters to slip through under your nose. Automating document verification and capturing liveness/biometric signals significantly hardens your front-door defences.
6. Sudden Account Activity
Accounts that were quiet then suddenly show high-value flows could indicate takeover, mule use, or funnel transactions. Such bursts of activity deviate from the account history and raise legitimate concerns that warrant immediate review. Your system should flag dormant-to-live transitions and trigger deeper evaluation of source, conduct, and destination.
7. Linked or Shared Accounts
When one individual or entity controls several accounts across your bank or network, risk multiplies. You may encounter parallel deposit streams, then aggregated outflows, indicative of funneling or layering schemes. Establish account linkage analytics to track relationships and patterns across multiple accounts and channels.
8. Cash-Heavy Transactions
Heavy use of cash deposits, travel-related funds, prepaid cards, or untraceable e-wallets increases laundering risk.
Criminals prefer these channels to avoid traditional banking traceability; your controls must account for them.
Integration of payment-rail intelligence and channel-specific thresholds is essential to keep your risk manageable.
9. Abrupt Behavioral Shifts
A customer shifting to a new business line, an unexplained product change, or a transaction type warrants immediate investigation. You may find the account was legitimate until illicit flows started; your detection remains a step behind. Regular refresh of risk profiles and behavioral baselines helps you spot divergence early and reduce blind spots.
10. Weak Ongoing Monitoring
Onboarding checks do not suffice; failure to refresh documentation, screen sanctions, or monitor transactions leaves gaps. When you’re relying on static thresholds or manual review only, you’re potentially missing evolving laundering techniques. Continuous monitoring, automation, and updating your controls are critical to stop red flags from turning into losses.
While these signals expose operational weaknesses, AML red flags uncover deliberate efforts to disguise illicit money flows within your system.
Also read: Understanding User Identity Verification Process
Key AML Red Flags to Watch For
AML red flags go beyond routine banking irregularities; they reveal deliberate attempts to disguise the movement and origin of illicit funds. Here are the distinct behaviors and transaction patterns that commonly signal active money laundering across your network.
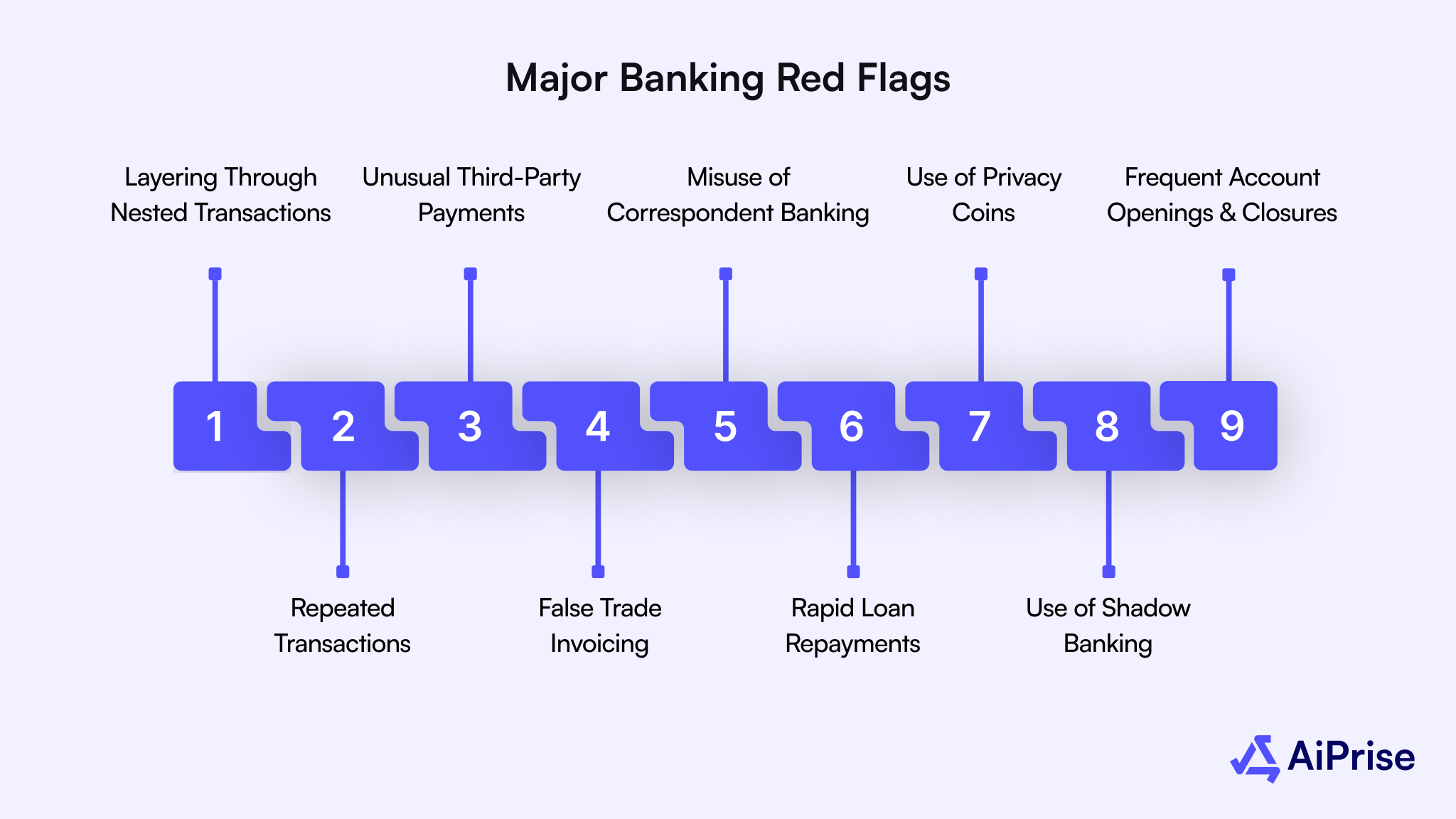
1. Layering Through Nested Transactions
Funds passing through multiple intermediary accounts or correspondent banks create confusion around their true origin. This pattern often involves deliberate “nesting” within larger institutions to conceal suspicious flows. Maintaining visibility across intermediaries and enforcing transaction look-through rules helps detect layering before funds exit your system.
2. Repeated Transactions Just Below Reporting Thresholds
Customers who consistently structure deposits or withdrawals to remain below reporting limits may be avoiding detection. This deliberate “smurfing” behavior fragments large sums into smaller transactions to bypass AML thresholds. Automated pattern recognition can identify repeated near-threshold movements that human reviewers might overlook.
3. Unusual Third-Party Payments
Funds transferred to or received from unrelated third parties without clear economic reasoning often indicate laundering channels. Such transfers exploit legitimate accounts as temporary pass-throughs for hidden beneficiaries. Reviewing payment relationships and validating counterparties strengthens your ability to uncover these covert transactions.
4. False Trade Invoicing
Trade-based money laundering disguises funds through falsified invoices or manipulated import/export values.
Criminal networks use this method to move money internationally under the pretense of commerce.
Analyzing pricing patterns, trade routes, and shipment data helps identify mispriced or circular trade transactions.
5. Misuse of Correspondent Banking Relationships
Nested relationships within correspondent accounts enable indirect access to your financial network through weak foreign controls. Illicit actors exploit these arrangements to obscure ownership and fund origins. Regular due diligence and transaction-level monitoring of correspondent partners mitigate exposure from external laundering activity.
6. Rapid Loan Repayments
Loans repaid unusually fast with unclear funds can legitimize illicit proceeds under the guise of early repayment. Such activity often lacks commercial logic and should prompt a closer review of repayment sources. Cross-referencing repayment data with customer income patterns ensures consistency and transparency.
7. Use of Privacy Coins
Privacy-focused cryptocurrencies and coin-mixing services conceal transaction origins and disrupt blockchain traceability. These tools fragment and reassemble funds to eliminate identifiable trails. Integrating blockchain analytics and crypto-risk scoring helps isolate high-risk wallets and detect laundering through digital assets.
8. Use of Shadow Banking
Unregulated money transfer systems, such as hawala or similar informal networks, enable anonymous cross-border movement of funds. These channels operate outside conventional oversight, complicating AML tracking and reporting. Enhanced scrutiny of cross-border remittance patterns helps identify and flag transactions routed through informal systems.
9. Frequent Account Openings and Closures
Opening multiple accounts across short timeframes and closing them soon after transactions indicates layering and concealment. This tactic removes traceability and limits the effectiveness of account-based monitoring. Centralizing customer data and enforcing cooling-off periods between account actions helps deter this behavior.
Identifying these laundering patterns is only effective when paired with structured actions that turn detection into a consistent compliance practice.
Practical Bank Playbook You Can Use This Quarter
A structured playbook helps you translate banking red flag detection into consistent, daily compliance practices across your institution. Here are key actions you can apply immediately to strengthen KYC accuracy, AML monitoring, and investigative outcomes.
- Establish a risk-based onboarding process that adjusts verification intensity according to customer type, geography, and transaction volume.
- Integrate document verification tools that authenticate government-issued IDs and cross-reference data against trusted registries automatically.
- Ensure beneficial ownership data is collected, verified, and linked to corporate structures before activating business accounts.
- Use transaction monitoring rules that align with specific customer risk profiles rather than relying on static thresholds.
- Configure alert prioritization to focus analyst time on complex, high-risk transactions instead of low-value false positives.
- Set up daily reconciliation between onboarding data and transaction activity to identify mismatches or missing due diligence fields.
- Train frontline and compliance teams to recognize behavioral indicators, such as evasive communication or inconsistent documentation.
- Conduct quarterly scenario testing to validate that systems detect patterns like funneling, layering, or rapid wire movements.
- Schedule periodic reviews of customer documentation, ensuring expired IDs, addresses, or business registrations are promptly updated.
- Document all red flag responses, escalation steps, and conclusions to create defensible audit trails for regulators and internal reviews.
With your short-term plays in place, maintaining long-term AML control requires consistency and collaboration, exactly what the next section explains
Also read: Online Identity Verification Methods: 7 Different Types
Common Compliance Gaps in Banking
Even with strong AML programs, small operational oversights can weaken your ability to detect critical banking red flags. Below are the most common compliance pitfalls that quietly increase exposure to fraud, regulatory penalties, and reputational risk.
- Outdated monitoring rules often fail to detect new laundering techniques or evolving transaction behaviors across digital channels.
- Fragmented data systems prevent analysts from connecting alerts across departments, leading to incomplete investigations and missed risks.
- Incomplete UBO verification leaves gaps that bad actors exploit through layered ownership and shell entities.
- Excessive false positives overwhelm analysts and delay the review of genuine red flags that demand immediate attention.
- Weak escalation protocols slow down responses when suspicious activity is detected, increasing regulatory and financial exposure.
- Infrequent document refreshes cause outdated customer information to remain in your system, masking new risks or ownership changes.
- Limited staff training reduces awareness of behavioral red flags and emerging fraud trends within your teams.
- Overreliance on manual reviews creates delays and inconsistencies that weaken compliance quality under heavy transaction volumes.
- Neglecting cross-channel activity causes blind spots when customers move funds between products or subsidiaries.
- Poor audit documentation limits your ability to demonstrate control effectiveness during examinations or enforcement reviews.
Closing these gaps is only part of the solution; reinforcing your AML framework ensures they don’t reopen over time.
AML Best Practices to Reduce Red Flags
Strong AML frameworks directly reduce the frequency and severity of banking red flags across your operations.
Below are key AML best practices to help you detect suspicious activity faster and maintain consistent compliance.
- Adopt continuous transaction monitoring to identify abnormal activity patterns as they occur, not after exposure has already occurred. Real-time detection minimizes financial loss and strengthens your ability to meet regulatory expectations during examinations.
- Align AML programs with FinCEN advisories and FFIEC guidelines to ensure every control meets current U.S. standards. Regular alignment keeps your institution ahead of enforcement actions and evolving regulatory interpretations.
- Automate sanctions and PEP screening to prevent onboarding of high-risk customers linked to illicit activity or restricted entities. Automated checks lower manual errors and shorten onboarding without compromising compliance accuracy.
- Review alerts collaboratively with fraud and risk teams to create a unified understanding of suspicious activity. Shared insights across teams help uncover patterns that siloed systems and departments may miss.
- Refresh AML policies and typologies annually to reflect emerging risks and new laundering methods observed by regulators. Updating policies keeps your framework adaptive and ensures analysts respond effectively to changing financial crime trends.
Applying these practices builds a sustainable foundation, and AiPrise’s capabilities make maintaining them far more manageable.
How AiPrise Supports Your AML and KYC Strategy?

AiPrise offers a full-stack platform that helps you proactively reduce exposure to banking red flags by combining KYC, KYB, AML, and fraud detection capabilities. Here are key features and services that align directly with the red-flag detection and compliance workflow we’ve discussed.
- Global Document & Identity Verification: AiPrise verifies over 12,000 ID document types and covers 220+ countries and territories, reducing onboarding risk worldwide.
- Biometric Authentication & Liveness Checks: The platform uses 1:N face-matching and real-time liveness tests to prevent identity fraud, impersonation, and synthetic identities.
- Comprehensive KYB & UBO Verification: AiPrise provides business-verification workflows, including global business lookups, ownership chains, and organizational structure to expose hidden controls.
- Risk-Scoring & Rule Engine: You can customize risk models and implement rule-based alerts aligned with your banking red-flags strategy, enabling faster escalation and fewer false positives.
- Continuous Monitoring & Sanctions Screening: The platform integrates watch-lists and adverse-media databases to continuously screen customers and flag elevated risk behavior beyond onboarding.
- Single API / Integration Layer: With one integration, you access multiple identity vendors and global data sources, simplifying your vendor stack and reducing complexity.
- Automated Workflow & Case Management: AiPrise automates document validation, identity checks, and case escalation so your team focuses on high-risk alerts, not manual reviews.
- Scalable Global Coverage: The platform supports complex compliance needs across jurisdictions and channels, ensuring that your monitoring of banking red flags adapts as your business grows.
Wrapping Up
Recognizing banking red flags early protects your institution from regulatory scrutiny, financial losses, and long-term reputational harm. Building proactive AML and KYC frameworks ensures that suspicious activity is identified, investigated, and reported before it escalates further. Embedding continuous monitoring, risk-based onboarding, and robust data validation helps you stay compliant while maintaining customer trust.
AiPrise empowers your compliance teams to detect, verify, and monitor risk seamlessly across every stage of the customer lifecycle. Its AI-driven verification, continuous screening, and automated case workflows reduce manual effort and improve detection accuracy in real time.
Book A Demo with AiPrise today to strengthen your AML defenses, simplify verification, and build a secure, compliant banking ecosystem.
FAQ
1. What are common banking red flags that indicate potential AML issues?
Common banking red flags include sudden large transactions, frequent small deposits, opaque ownership structures, and transfers to high-risk jurisdictions. Identifying these patterns early allows your compliance team to investigate and report suspicious activity before losses occur.
2. How often should banks update their KYC and AML records?
KYC and AML records should be refreshed every 12–24 months for standard-risk customers and more frequently for high-risk ones. Regular updates ensure that customer profiles, ownership data, and transaction patterns remain accurate and regulator-ready.
3. What documents are essential for verifying individual and business customers?
Essential documents include a government-issued photo ID, proof of address, and, for businesses, incorporation certificates and beneficial ownership details. Collecting and verifying these documents strengthens your compliance posture and prevents fraudulent or high-risk account openings.
4. How does continuous monitoring help in detecting banking red flags?
Continuous monitoring tracks real-time activity to identify unusual behaviors that static reviews might miss. This approach ensures faster detection of suspicious transactions, better risk control, and improved overall compliance outcomes.
5. How does AiPrise improve AML and KYC compliance for banks?
AiPrise automates ID verification, sanctions screening, and ongoing monitoring through AI and machine learning. These capabilities help your institution detect red flags faster, reduce false positives, and maintain full regulatory compliance effortlessly.
You might want to read these...

AiPrise’s data coverage and AI agents were the deciding factors for us. They’ve made our onboarding 80% faster. It is also a very intuitive platform.